This is an archive page. What you are looking at was posted sometime between 2000 and 2014. For more recent material, see the main blog at https://laboratorium.net
The Laboratorium
June 2008
Why the Precautionary Principle Is Bunkum
Via /nev/dull, Shtetl-Optimized - Blog Archive - Better safe than sorry:
Given our present state of knowledge, we simply cannot exclude the possibility that aliens will visit the Earth next year, and, on finding that we have not yet produced a Higgs boson, find us laughably primitive and enslave us. Or that a wormhole mouth or a chunk of antimatter will be discovered on a collision course with Earth, which can only be neutralized or deflected using new knowledge gleaned from the LHC. Yes, admittedly, the probabilities of these events might be vanishingly small, but the fact remains that they have not been conclusively ruled out. And that being the case, the Precautionary Principle dictates taking the only safe course of action: namely, turning the LHC on as soon as possible.
I would add that it has not been conclusively ruled out that the aliens will find us and enslave us for adhering to the Precautionary Principle, and on that ground alone, we must reject it.
As Runoff Nears, a Grim Image of Politics in Zimbabwe Emerges - NYTimes.com:
One of Mr. Tsvangirai’s most senior aides, Tendai Biti, was freed Thursday on bail of a trillion Zimbabwean dollars, or about $90. He was arrested two weeks ago on treason charges, which carry a potential death penalty.
If You Think Legal Citation Is Hard These Days …
As for statutes, problems had developed with the citation of acts by the regnal year of the parliamentary session in which they received the royal assent. Perhaps borrowing from the bibliographic reference, some attorneys encountered problems because they would declare that a statute had been enacted in, for example “2 and 3 E. 6.” The courts held that an act cannot be passed in two years, and consequently the variance was fatal. On the other hand, one lawyer, perhaps aware of some of these cases, tried to cite an act as 4 Philip and Mary. But Mary had been queen regnant for a year before she married King Philip of Spain, who was made titular King of England. So the first year of Philip was the second year of Mary, and there could be no fourth year of Philip and Mary. The act should have been cited as 4 and 5 Philip and Mary. No less a judge than Lord Mansfield held the citation a fatal variance, although he was apologetic.
—Byron D. Cooper, Anglo-American Legal Citation: Historical Developments and Library Implications, 75 L. Libr. J.3 (1982)
Newsweek is a National Embarassment
Via /nev/dull, The $10,000-a-Month Psychic | Print Article | Newsweek.com:
“When Seagate Technology, the $11 billion-a-year maker of hard drives for the Playstation 3 and Microsoft Xbox, went searching for a consultant to run one of its management workshops in the fall of 2006, it bypassed the usual list of Silicon Valley gurus. Instead, Seagate’s executive director of software engineering, Gabriel Lawson, invited Laura Day—a stylish New Yorker with no tech experience—to train his Colorado-based team. ‘She was amazing,’ Lawson tells NEWSWEEK, recalling Day’s quick insights into the poor coordination between the company’s research and marketing teams. ‘Anybody who can afford her will get 100 times their money’s worth.’ What exactly is Day’s expertise? While she likes to downplay it as mere ‘intuition,’ her clients prefer another explanation: she’s a psychic.
Tony Dokoupil manages to write 1,200 words in Newsweek about professional psychics without once telling his readers the single most relevant fact: Psychic powers don’t exist. Would Newsweek run an interview with the Easter Bunny? Would it let Jane Bryant Quinn suggest investing in perpetual motion machine startups? Would it print travel tips for hitching a ride on a flying saucer to Neptune? But here it is, an article whose sum and substance is that hiring a psychic could do wonders for your business.
This article is professional malpractice. No competent journalist would ever write something this brazenly, obviously, mendaciously misleading. If Dokoupil’s editors are responsible for the credulity, he should have taken his byline off of the article. By putting his name to it, he told the world, I, Tony Dokoupil, am unfit to commit acts of journalism. If this is what passes for professional reporting, what right does anyone have to complain about the quality of blog-based reporting?
News magazines have a basic duty to distinguish between things that are plausible and things that are not. If Newsweek isn’t going to fulfill that duty—and it’s not hard, as duties go—it should do the public a service and close its doors. People who read the June 30, 2008 issue of Newsweek will be negatively informed. They will know less about the world when they finish reading it than they did when they started.
Trash like this is why we let our subscription lapse.
Link by Link - Delaying News in the Era of the Internet - NYTimes.com:
“Looking at the detailed records of editing changes recorded by Wikipedia, it quickly emerged that the changes came from Internet Broadcasting Services, a company in St. Paul, Minn., that provides Web services to a variety of companies, including local NBC TV stations.
An I.B.S. spokeswoman said on Friday that ‘a junior-level employee made updates to the Wikipedia page upon learning of Mr. Russert’s passing, thinking it was public record.’ She added that the company had ‘taken the necessary measures with the employee and apologized to NBC.’ NBC News said it was told the employee was fired.”
Securities fraudster Henry Blodget adds:
Fired?
If the employee learned the news because NBC was officially distributing it to affiliates under embargo, that’s one thing (the firing would be appropriate). If the employee heard about it unofficially, however, from friends at NBC or I.B.S., then the firing was outrageous. …
The world has changed in last 15 years, and the genie isn’t going back in the bottle. If NBC wants to maintain its tradition with respect to staffers’ deaths, that’s fine. In the meantime, it should recognize that its chances of controlling a story this big are—and should be—infinitesimal and that “citizen journalism” has long since gone mainstream. If the employee at IBS who updated the Wikipedia entry did not learn of it via a confidential NBC communication, moreover, NBC and IBS owe him or her an apology and a job.
This is where the old me and the new me part ways. The old me—the irascible programmer—would say that Blodget’s rule is right. They can fire you if you break a confidence; they can’t fire you if you don’t. The new me—the irascible lawyer—would say that even if that rule is the ideal one, we may never know whether the I.B.S. employee acted on confidential or publicly-known information may be extremely hard. Blodget says “If the employee … did not learn of it via a confidential NBC communication,” as though we could simply flip open the Book of Facts and get a yes-no answer. What if the employee learned of it through office gossip from a coworker who read a confidential dispatch from NBC? What if the employee read a confidential dispatch, and then heard about the news on Twitter? What if the employee says the information came from Bob, and Bob doesn’t remember where he heard? What if there are no clear further facts at all, and no one can reconstruct the chain? The old me would have been willing to chase these hypoes out a lot further. The new me says at some point we throw up our hands.
One of my students this semester wrote:
You have read this eval; now you must send 130 evals to other professors or you will get no luck.
Have I mentioned recently how great my students are?
Packet Injection as Infringement
Free Press and Public Knowledge have just released an important new report, NebuAd and Partner ISPs: Wiretapping, Forgery and Browser Hijacking. In it, they provide strong evidence that NebuAd injects cookies into web pages without the knowledge of either the sender or the recipient of the page. Wired’s Ryan Singel has a good run-down:
NebuAd first drew widespread attention after Charter Communications, the nation’s fourth largest ISP, announced it would try out the company’s technology, promising that users would love having more targeted ads served to them. That announcement brought unwanted media and congressional attention to NebuAd, which had already installed monitoring boxes inside the network of at least one smaller ISP, WOW.
NebuAd has conceded that its boxes peer deep into internet packets to pull out URLs and search terms in order to classify each user’s interests. That profile is then used deliver tailored ads on various partner websites.
But Free Press and Public Knowledge found that sometimes when a WOW subscriber visited Yahoo or Google, NebuAd faked an additional packet of data that appears to be the last part of the downloaded Google webpage. The extra packet included NebuAd-written JavaScript that directs users’ browsers to a NebuAd-owned domain named faireagle.com, where the company drops tracking cookies from other domains and companies on the user’s computer. These can be used later to deliver customized ads based off analysis of where people have gone on the web or what search terms they have used.
When this kind of “deep-packet injection” is done to a web page from a NebuAd partner, the level of surveillance is creepy, but the consent of the web page provider eliminates some of the legal concerns. In that scenario, NebuAd is just an ad-serving network on steroids; by sitting closer to the end-user in the network, NebuAd could dial up the quality of the ad targeting another few micro-notches. Things are much more troubling, however, when—as the report concludes—NebuAd injects its code into the web pages of unsuspecting third parties. Now, not only is the user in the dark about this skulduggery, but so its the web page owner whose consent was previously being used to legitimize the practice. And that shift could mean serious legal trouble.
It should be obvious that there may be privacy issues with this practice; in order to inject its cookies and ads, NebuAd must look very closely inside your Internet traffic to know when you’re loading a web page it could insert them into. That is, every instance of deep-packet injection must have been accompanied by an instance of deep-packet inspection. Declan McCullagh has a good discussion of whether that would violate the Electronic Communications Privacy Act, the Communications Act, and the Cable TV Privacy Act. The short answer is that a great deal depends on how meaningful the user’s consent to the practice is.
I’d like to raise another set of issues that NebuAd-style deep-packet injection raises: the threat of copyright and trademark liability for NebuAd, its advertisers, and its partner ISPs. The basic point is that almost any web page from a commercial site will contain copyrighted content and trademarks owned by the page’s provider. Take Amazon. Its layout is copyrighted (more dramatically, so are the news stories on the New York Times’s side). Its page also contains its logomark, the wordmarks AMAZON and AMAZON.COM, the trademarks associated with various Amazon products and services (e.g. KINDLE), and its distinctive layout and design, which function as identifying trade dress. Altering the page in-flight, without Amazon’s consent, could give Amazon grounds to sue.
Start with copyright. Ordinarily, the actions of any ISP in delivering web content to you are completely and utterly shielded from copyright liability by 17 USC 512(a). But one of the conditions of 512(a)’s immunity is that “the material is transmitted through the system or network without modification of its content.” Whoops. Tim Wu pointed out this one. The counterargument, I suppose, would be that the immunity still applies to every part of the page that NebuAd doesn’t change. I wouldn’t bet my ISP business on that one; the more natural reading of 512(a)(5) is that one looks at “material” as a whole to see whether its “content” has been modified, not that one slices the “material” into modified and unmodified parts. Since an ISP would be obviously and directly liable for any copyright infringement in any material it itself inserted, the ISP-friendly reading of 512(a)(5) would make that language superfluous.
The ISP’s other defense to copyright infringement would be that Amazon provided it with a license to transmit the page by responding to the user’s request for it. Just as Amazon is giving the user a license to download and view the page, the ISP would say that Amazon is giving it a license for the transmission. Perhaps. But it seems logical to say that the license Amazon gives the ISP is to transmit the page in the form Amazon provided it. By changing the page, the ISP exceeds the scope of its license. Amazon could also always be more explicit about its license, for example by sending a warning letter to the ISP.
The bottom line is that an ISP trying out this technology should be very concerned that at least one of the web sites caught up in the net will be angered enough to bring a copyright lawsuit. The lawsuit might or might not succeed, but the legal risks are serious. NebuAd, as the company supplying the ISP with the technology that makes these changes, would be at risk as well, as one or more of a direct, a contributory, a vicarious, or an inducing infringer. More strikingly, NebuAd’s advertisers might even be at risk: that would depend on how much they knew about what NebuAd was doing on their behalf and how they benefitted from its actions. It’s a longer shot, but I can’t imagine that advertisers would be happy with any legal risk from their choice of ad-serving partners.
Trademark law is, if anything, even more dangerous for NebuAd. The problem here is what trademark lawyers call “passing off.” The classic form of passing off is giving a customer who asked you for a Coke your house-brand cola instead. The harm consists in using your competitor’s trademark (and all the trust people have in it) to pass off your own goods on consumers.
When an ISP delivers a page to a user, there’s an implicit statement involved: “This is the page you asked for.” If you typed in “nytimes.com,” you don’t want to see the Fox News homepage, you want the New York Times. When your ISP delivers you a page with a NebuAd cookie injected, the statement that this is the page you asked for is false. The ISP is passing off the NebuAd cookie as being from Amazon. It’s not.
Yes, the cookie isn’t directly something you’re paying for, like the cola. But I think it’s close enough that trademark law would say, “Hey, knock it off!” The cookie is used in selling you other goods (since profiling for ad targeting is NebuAd’s business model). More importantly, when you run a web browser, you decide which cookies to allow and which ones to block. I’ll let Amazon set a cookie; I trust them enough. I won’t let malware.ru set a cookie; I don’t trust them. I express this difference in trust, in part, by pointing my browser to amazon.com but not to malware.ru. NebuAd’s packet injection blows away this safeguard. It tricks me into accepting a cookie I wouldn’t have otherwise wanted. That’s a misuse of the Amazon trademark (in particular, of the amazon.com URL).
There’s also a common-law unfair competition problem. Amazon does work in making its site attractive and useful. That work convinces consumers to visit amazon.com. Amazon then turns those site visits into money by selling things and by profiling its users. Other sites that invest in attracting users make money by showing ads. When NebuAd and its parters come along and use Amazon’s site visits to build better ad profiles, there’s a strong argument that they are “reaping where they have not sown.” That is, they’re free-riding on the relationship between Amazon and its users. This end of IP law can be a little murky, but were I NebuAd, I’d want my lawyers to look very closely at the case law.
All in all, I’d say that NebuAd opens up some unpleasant cans of worms by injecting cookies. (And I’m not even getting into the security concerns, or the privacy issues!) While I’m not entirely happy that IP law reaches as far as it does, given that it does, companies like NebuAd need to tread carefully. Injecting cookies into traffic from unsuspecting websites seems like a very risky step.
Oregon Does Right, Drops Copyright Claim in Its Laws
“Oregon’s Legislative Counsel Committee had a meeting this morning to discuss the copyright claim on the Oregon Revised Statutes. After taking legal counsel from Dexter Johnson, talking with Karl Olson, Carl Malamud, three Oregon citizens and myself, they unanimously voted to not to enforce any copyright claims on the Oregon Revised Statutes. This great!!!”
(Via BoingBoing.)
Lil’ Gabe is 3 and a half now and so it’s very important that we always have a ready supply of fruit snacks. If we’re out shopping or at the bank or whatever, fruit snacks have the ability to soothe the savage three year old. We like to let Gabe pick out his own fruit snacks and he usually will choose Spider-Man or maybe SpongeBob. However I came home recently and found these in the pantry.
I would love to know what sick bastard at Kellogs came up with this genius idea. I just spent the first three years of my sons life trying to get him not to eat blocks, and now you’re telling him they taste like fucking strawberries. Thanks a lot assholes. Seriously, how in the hell did this ever get past their legal department. You can’t tell me that this isn’t a lawsuit just waiting to happen. I can only assume that their next product is fruit flavored thumbtacks.
It’s an interesting problem from a products-safety-law point of view. The Lego Fun Snacks are harmless in themselves. They just make Legos dangerous.
Remind Me Why We Went Electronic?
I voted in the New Jersey primary a couple weeks ago. I used an electronic voting machine. It was not a reassuring experience.
After signing in the voter roll for my district, I was given the usual slip to hand to the poll worker at the machine. She threaded it with a needle, along with the previous slips, pushed a few buttons on a side panel, and invited me to go in.
Once inside. I pushed the button next to my chosen senatorial candidate. The green X came on. Then it went out. I pushed the button again. The X came on, then blinked out after a second. I tried a third time. On, then off.
I stepped out of the booth and told the worker that the X was lighting up but then immediately went off. She was puzzled, and went back to the voter roll table to consult her colleague there. Aha, she was told, you need to push the button to set the appropriate party primary. So she came back, did something on the machine’s controls out of my sight, and told me to go back inside. So I stepped back in the curtains, pushed the button again, and watched the X light up—before going off, just like before.
I told the worker it wasn’t working; a brief conversation ensued outside. Then she did something else, and the lights came on inside the curtain. (I hadn’t even realized that I’d been voting in the “dark”; it’s not a very bright light.) This time, when I pushed the button, the X stayed on. So did the Xes for the other candidates whose buttons I pushed. With everything now appearing to be in order, I pushed the big button to record my vote and went on with my day.
Some thoughts:
- I am less confident that my vote was properly recorded than in any other election I’ve ever voted in. Having someone tinkering with the machine while you’re in the process of voting is especially disconcerting.
- If I hadn’t noticed that something was wrong with the X, my vote definitely wouldn’t have been counted. Why did the X come on at all if the machine wasn’t ready to receive my vote?
- There were no instructions provided to tell me to make sure that my Xes stayed on. The light is a useful signal that the booth is active, but the absence of the light doesn’t clearly signal the reverse.
- How many other people at this polling place had their votes not counted because of this poll worker’s mistakes prior to me? How many other poll workers made similar mistakes? Someone should pull the voting records and compare the number of signatures in the voter roll to the total number of ballots cast at the corresponding machines.
The Princeton team has been doing yeoman’s work on keeping New Jersey e-voting honest. My experiences underscore the importance of that cause.
Copyright, Technology, and Access to the Law
I’ve just released Copyright, Technology, and Access to the Law: An Opinionated Primer:
Recently, the state of Oregon has used copyright law to threaten people who were publishing its laws online. Can they really do that? More to the point, why would they? This essay will put the Oregon fracas in historical context, and explain the public policies at stake. Ultimately, it’ll try to convince you that Oregon’s demands, while wrong, aren’t unprecedented. People have been claiming copyright in “the law” for a long time, and at times they’ve been able to make a halfway convincing case for it. While there are good answers to these arguments, they’re not always the first ones that come to hand. It’s really only the arrival of the Internet that genuinely puts the long-standing goal of free and unencumbered access to the law within our grasp.
This isn’t an academic piece. Instead, it’s designed to bring nonlawyers and people outside the open-access-to-law movement up to speed on the basics of the history, the context, the principles, and the law. Along the way, it tells some interesting stories. I hope you’ll find it equal parts informative, entertaining, and inspirational. Please have a look.
UPDATE 2008-06-24: Ed Felten has a good blog post running through the policy implications in a page.
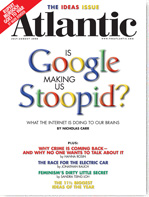
Nicholas Carr, Is Google Making Us Stupid?:
Taylor’s system is still very much with us; it remains the ethic of industrial manufacturing. And now, thanks to the growing power that computer engineers and software coders wield over our intellectual lives, Taylor’s ethic is beginning to govern the realm of the mind as well. The Internet is a machine designed for the efficient and automated collection, transmission, and manipulation of information, and its legions of programmers are intent on finding the ‘one best method’-the perfect algorithm-to carry out every mental movement of what we’ve come to describe as ‘knowledge work.’
Taylorism isn’t the right metaphor for what Carr is trying to say. The rest of his argument is that Google (and other Internet technologies) are making us scatterbrained and unable to do one thing for sustained periods of time. Yes, Taylorism and the Internet are both built around shattering things into their smallest divisible units, but there the metaphor fails. Taylorism is a process of standardization, uniformity, and repetition—the opposite of the trend Carr is describing.
Overall, it’s a weak piece. While it’s better-written and slightly more convincing than other entries in the genre of “warnings about Internet cognition,” there’s nothing in it that I haven’t seen before. He shuffles the deck into a different order, but it’s still the same old cards.
I will say that cover design for the story is clever. The color choices in “Stoopid” are uniquely determined by the colors Google chose for “Google.” Here’s why:
- The left “o” must be red and the right “o” yellow, both to match the “o”s in “Google.”
- The “S” must be blue, to match the “G.” (Both are capitalized and at the start of the word.)
- The “t” must be green, because no other color works. Blue is out because that would be two blue letters in a row; red is out for the same reason. Yellow would result in two yellow letters flanking the red “o,” which would be suboptimal.
- The “p” must be blue, to match the “g.” (Both are immediately to the right of the “o”s and contain the only descender in the entire word.)
- At this point, two different factors suggest that the “i-d” sequence should be green-red. First, it matches the sequence in “Google,” which ends green-red. Second,the choices thus far set up a color cycle in “Stoop”: blue-green-red-yellow, then begin again with blue. Continuing the cycle gives us green-red.
- The color cycle is now so strong that yellow is a natural follow-on for the question mark. Note also that yellow is the lightest color, so it’s the least obtrusive one to use for the “extra” question mark that follows the end of the word.
In Which I Defend Cindy McCain
David Weiner: Re-Heat Offender: Cindy Bakes Another Whopper - Politics on The Huffington Post (via Joe Gratz):
Here we go again. Just two months after we broke Recipegate comes news that Cindy McCain is up to her old tricks. The July 2008 issue of Family Circle featured an article in which each (it went to press before Hillary conceded) of the presidential candidates’ significant others submitted a cookie recipe. A tipster caught a whiff of something besides sugar after reviewing Cindy McCain’s Oatmeal-Butterscotch cookies, and quickly found the original recipe at Hersheys.com (see image below). While McCain, or that same low-level staffer, managed to take the time to switch a few minor details in her version of the recipe this time around, there is no doubt that the recipes are the same.
While Bill Clinton gives credit to the family cook, and Michelle Obama to the godmother of her daughters, Cindy McCain attributes her cookie recipe to “a good friend.”
Unless John McCain was a childhood friend of Milton S. Hershey or her beer baron family worked with him on a chocolate beer bar back in the day, it seems Cindy is a plagiarist of the most delicious kind. Again.
The last claim doesn’t automatically follow. Cindy McCain could have gotten the recipe from a good friend, who took the recipe from Hershey’s. Insert more links in the chain if you want. The point is simply that she well may have discharged her duty of attribution. The main reason to doubt that story is the McCain campaign’s history of passing off other people’s recipes as Cindy’s. Last time, they blamed an intern. If this years most common campaign scandal pattern runs its course again, the McCain campaign will find one of her friends to step forward, admit borrowing the Hershey’s recipe, and claim to be the “good friend” who gave it to Cindy.
Just Another Tuesday Night at Home
“If I did emergency medicine, I’d feel confident that if I were on a plane and they asked for a doctor, I’d be able to do something useful.”
“Whereas, if you did, say, psych … “
“Well, I’d be useful if someone were trying to hijack the plane.”
“You could be all like, ‘So you’re telling me that you want to hijack the plane. Tell me more about that.’”
“Do you dream about hijacking planes?”
“Do you really want to hijack the plane, or is hijacking planes about pleasing your distant father?”
“Does this inkblot look like a plane to you?”
“Do you hear voices telling you to hijack planes?”
“I’ll say a word, and you say the first thing that comes to mind. Hijack.”
“Is there a history of hijacking planes in your family?”
“Do you need to hijack a plane to get started in the morning? Do you feel guilty about hijacking planes? Do you get annoyed when people criticize you for hijacking planes? Have you ever tried to cut back on hijacking planes?”
“Can you spell ‘plane’ backwards for me?”
“Have you ever taken Ambien and woken up hijacking a plane?”
Mike Davidson - Apple Just Killed The Market for Phones:
At the risk of sounding like a fanboy of the highest order, how on earth could the average customer justify purchasing any other mobile device at this point? If you can still get a free phone somewhere and that suits you, then great. But for the person thinking of spending between $99 and $799 on a Nokia, Motorola, Palm, or Sony, how can you even think about those alternatives given where the iPhone just went? The quality/feature/usability gap is so large that even a hatred for AT&T can’t keep people away now.
I have to demur. Granted, the iPhone is great already, the App Store will unleash amazing things, and the pricing shows that Apple is gunning for much larger market share. But even if you think that Apple design is objectively better, not everyone likes it. Many people use Vista voluntarily.
In particular, the no-buttons thing is an absolute dealbreaker for some people. Students typing no-look text messages under their desks come to mind. People scared by complexity who just want a phone that dials do too. And so do rocket-thumbed business email addicts. Some people just like buttons. And the other cell-phone companies will still have a good-sized line of business serving them.
(Via Daring Fireball.)
Citizen Journalism, on Your iPhone
Big news from the Steve Jobs keynote at WWDC. Here’s MacRumors’s one-liner:
10:41 am [The Associated Press] call it the Mobile News Network, and it gathers content from many trusted sources. It makes use of the location API by automatically showing nearby sources. Allows news video and photos to be viewed directly through the app. You can even report on news yourself by sending a first-hand report that includes photos and text. The app will be free at the launch of the App Store. (emphasis added)
This is cool on a whole different level than being able to play Super Monkey Ball on your iPhone. This is an amazing platform for citizen journalism, and it’s being delivered by one of the major names in news. Much will depend on what happens to those “first-hand reports,” but if the AP runs with this ball, it could be huge. Imagine an army of citizen-journalists, not just routing around the traditional media, but reporting with them. This is what happens when you give people general-purpose computers, portable anywhere, and hooked up to a worldwide network: amazing things are possible.
Why, Oh Why, Can’t We Have a Better Book Review Corps?
Lucy Ellmann’s review of Chuck Palahniuk’s Snuff in the New York Times Book Review opens:
What the hell is going on? The country that produced Melville, Twain and James now venerates King, Crichton, Grisham, Sebold and Palahniuk. Their subjects? Porn, crime, pop culture and an endless parade of out-of-body experiences. Their methods? Cliché, caricature and proto-Christian morality. Props? Corn chips, corpses, crucifixes. The agenda? Deceit: a dishonest throwing of the reader to the wolves. And the result? Readymade Hollywood scripts.
No honest book review—one that adds to the human store of knowledge about literature rather than subtracts from it, one that informs inform its reader about the book in question rather than misleads her, one that provides good reasons to read nor not to read the book rather than empty verbiage—no piece of writing, in short, that is honest, that is about the book, and that is actually a review, begins like this. I carry no particular water for Chuck Palahniuk, and indeed the Amazon hive-mind has decided that Snuff is the weakest of his novels, but no novelist deserves a review this mendacious, this ill-informed. It’s a hack job of a hatchet job.
Crime? Try Pudd’n’head Wilson. Out-of-body experiences? How about The Turn of the Screw? For that matter, what about the following dust-jacket description of Ellmann’s own Dot in the Universe:
After a brief sojourn in the underworld (populated by “underaged, underdeveloped underlings all, understated in their undershirts and UNDERSTANDING VERY LITTLE”), Dot is reincarnated, first as a possum, and then as a girl in Ohio.
If the New York Times Book Review continues to publish this junk, I give it ten years at the most.
Live Comment Preview from New York
I’ve added live preview to the comment form. Your comments now appear beneath the entry field, in real-time, formatted as they will be once you hit “Post.” And yes, it still understands both HTML and Markdown. These nifty features, plus the elegant, lightweight interface, come to your courtesy of WMD.
Enjoy!